With each passing year, newer technologies emerge and companies of all sizes adopt them to keep up the competitive, ever-changing…
News & Trends
View AllEver heard of the butterfly theory? A single flap of a butterfly’s wings in Australia has the potential to cause…
Latest
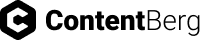
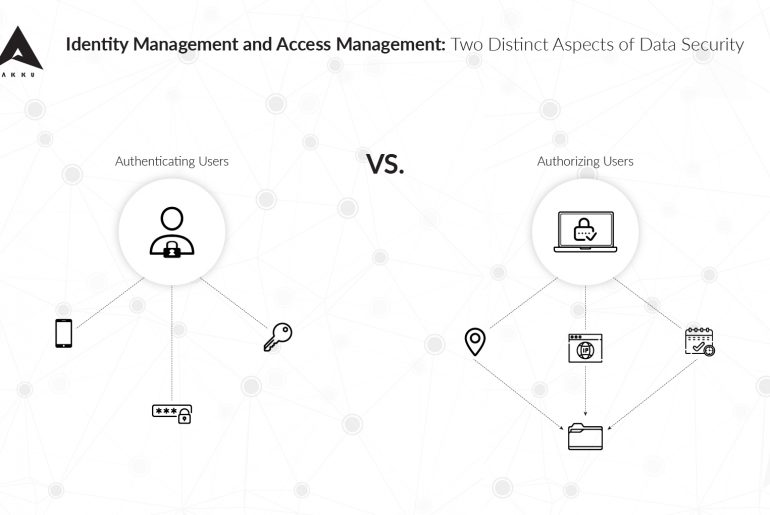
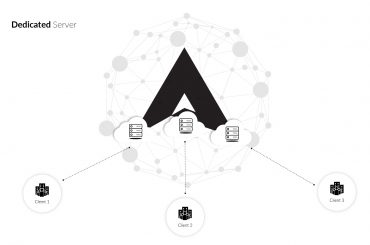
For organizations, it is crucial to ensure data security and, therefore, IAM has become a crucial part of every network security effort. Identity and access management at the organization-level – mostly include IAM solutions for enterprise applications used by organizations to authenticate and validate employees and a relatively small number of users. But how different is the situation with B2C businesses and other organizations who have huge numbers of internal and external users using their online services every day?
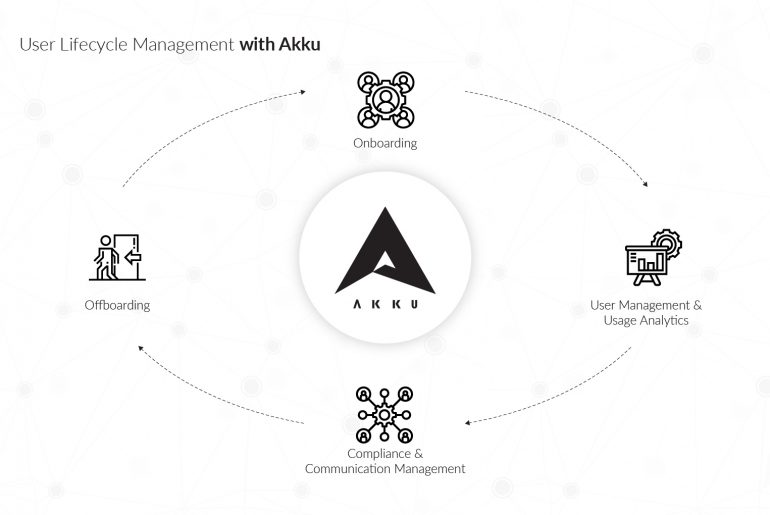
The employee lifecycle is an HR model that identifies the different stages an employee goes through during his/her stint at an organization. Employee lifecycle management, therefore, involves the steps taken by HR in optimizing the flow of the cycle. Typically, the employee lifecycle involves the following stages: recruiting, onboarding, training and development, retention, and offboarding.
In modern organizations, where the employee is also a user (of one or more applications), a similar user lifecycle begins at the onboarding stage and continues until the employee exits the organization.
Online identity theft, simply put, is impersonation on an online platform. If someone else pretends to be you — either by stealing your credentials and logging into your account or by creating a fake account that others believe is yours – then your identity has been stolen.
There are a number of ways – data breaches, phishing, mishandled passwords, and more – through which personal data collected by an organization can be compromised, giving rise to the risk of identity theft. There are also a number of ways in which Akku, the Identity and Access Management (IAM) solution by CloudNow, can help you prevent it.