The manufacturing industry took a big hit at the start of the pandemic-imposed lockdown, mainly due to two reasons. Firstly,…
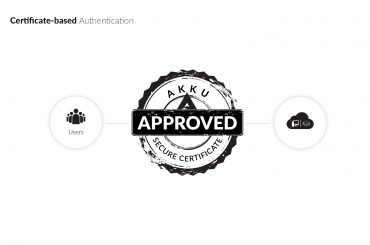
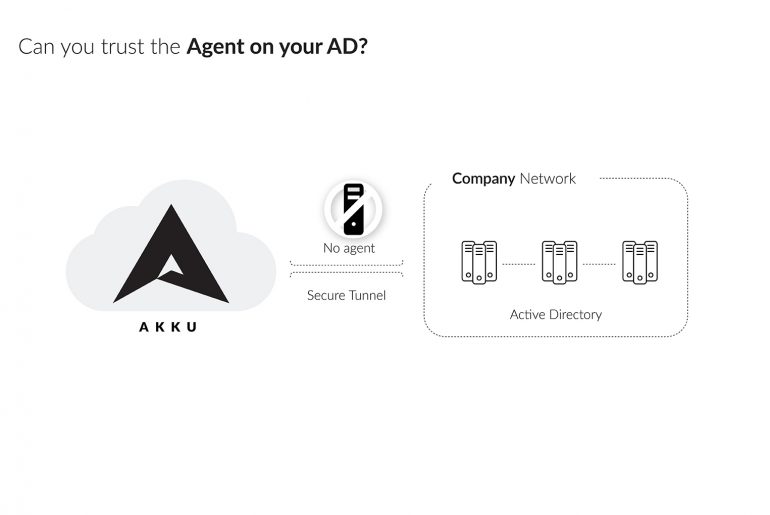
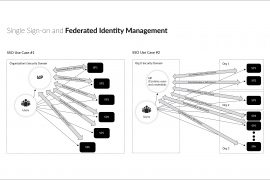
If a company works with very few applications, user repositories would have to be mapped individually for each application. Every…
Latest
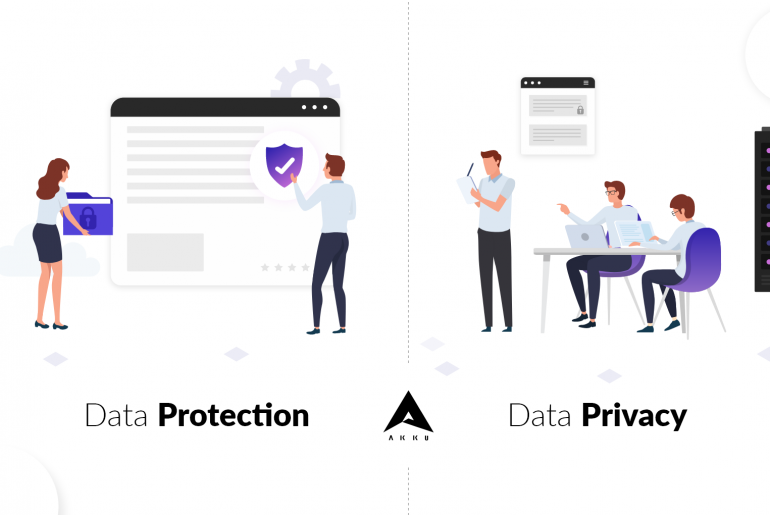
Data protection and data privacy are so closely linked that people (and sometimes even organizations) tend to think of them as synonyms. However, understanding the difference between the two is crucial to ensuring that both protection and privacy are maintained.
The Health Insurance Portability and Accountability Act (HIPAA) has been effective in the USA since 1996.
The Act actually has five different section titles, namely Health Insurance Reform, Administrative Simplification, Tax-Related Health Provisions, Application and Enforcement of Group Health Plan Requirements, and Revenue Offsets – however, the mention of ‘HIPAA Compliance’ most often refers to compliance to the second title – Administration Simplification.
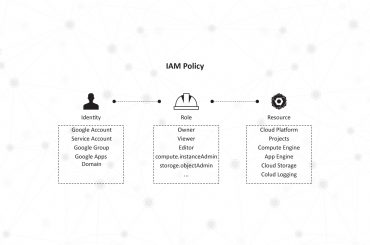
Technology users today are spoilt for choice when it comes to the types of devices and the variety of platforms through which they can stay connected to work and social groups. They can access their accounts from simply anywhere and at any time, as long as they can authenticate their identities.
However, the process of authentication as we know it has remained largely static – the user provides the system with their credentials at the time of access, the system matches it against its database of user data and provides the user access to the network on successfully validating their credentials.