When an enterprise migrates to the cloud, it essentially opens the doors to a range of new possibilities for its business to flourish. When cloud capabilities are utilized to their full potential, several aspects of management are largely simplified, various processes integrated, and employees empowered to focus on their core roles.
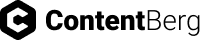
However, many of these benefits to efficiency and convenience are often rendered ineffective by the roadblocks that tight security systems bring into the mix. That is why it is important to take into account the impact of your user, data and application security set up on user experience across your environment.
Company X is a leading insurance company which provides laptops to all employees for their work, regardless of their grade…
Latest
“irgvctxmsr” – sounds like gibberish, doesn’t it? But if you were to decrypt this string using a mono-alphabet shift cipher where each letter has been shifted to the right by 4 numbers, you would see that it spells “encryption”!
Protecting critical data and information by encrypting them was first performed by Julius Caesar in 120 BC. The art of encryption has been through several modern shifts, and currently most of the data on the internet is protected using sophisticated encryption algorithms like AES (Advanced Encryption Standard), RSA (Rivest-Shamir-Adlemen), ECC (Elliptic Curve Cryptography) and PGP (Pretty Good Privacy).
A brute-force attack is a type of cybercrime which involves automated hacking activity using bots. The primary aim of a brute-force attack is to crack a password in order to gain access to a user account in an unauthorized manner. Using the automation tool, an attacker repetitively attempts different alpha-numeric combinations at considerable speed – thousands per second – until the user’s password is determined and the account is unlocked.
With the advent of the cloud and the rapid innovations in technology, a brute-force attack has emerged as one of the most common types of outsider attack against web applications.
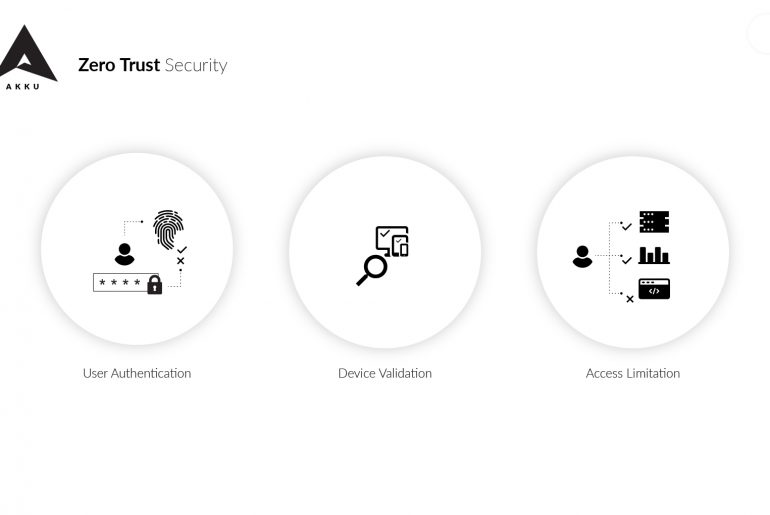
As organizations increasingly place their data and applications across multiple locations on the cloud, zero trust security is rapidly gaining ground as the network security model of choice among enterprises.
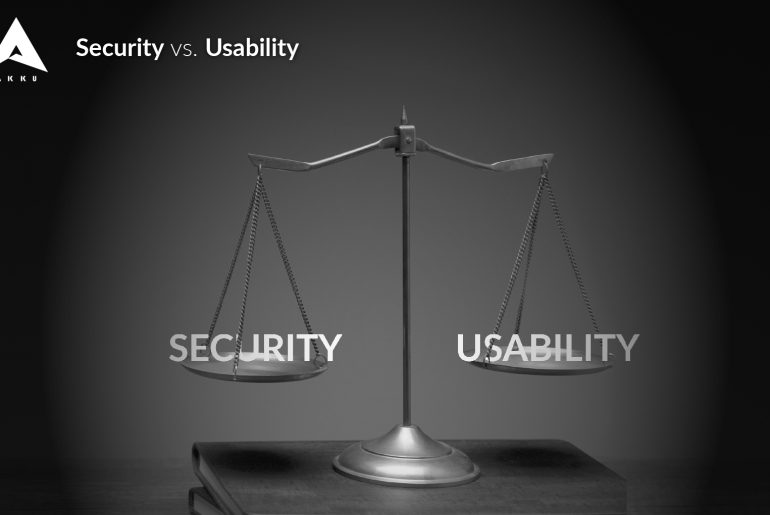
Zero Trust Security is a security model in which a user, irrespective of whether he/she is within or outside the network perimeter, requires an additional verification to get access into a network. There is no particular technology or software product associated with this security model. It simply requires an additional security layer to verify users. This could be anything from biometric verification like thumb-print scanning, or a digital signature verification. Of the two, biometric verification is preferable as it can neither be recreated nor hacked.