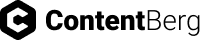
Identity management encompasses several operational mechanisms for managing users across a large system or network of applications. Two of the most prominent of those are Single Sign-on (SSO) and Federated Identity Management. Due to its evolving nature, identity and access management has several terms thrown around ambiguously. Even among developers, major differences are often missed while talking about federated identity and SSO. In this article, we aim to break down the difference between the two.
One of the main reasons for a number of traditional, older enterprises still being wary of cloud computing is the concern they have over the security of their data on the cloud. There are a number of myths surrounding cloud security that make it difficult for many enterprises to take the plunge and undertake cloud migration to leverage the many benefits of the cloud.
Here are a few of these myths, and why you should stop believing them!
Governments across the globe rely increasingly on technology today to serve their citizens better. But with the rapid evolution of technology, it is often a struggle for the different departments of government to keep up. This happens due to insufficient funds, security concerns or simply a lack of motivation to meticulously plan and implement the move.
Of these, security is the most critical consideration, since government agencies and departments are possibly the first line of defense against any cyber attack. This is especially true when it comes to government entities wanting to migrate their operations to the cloud.
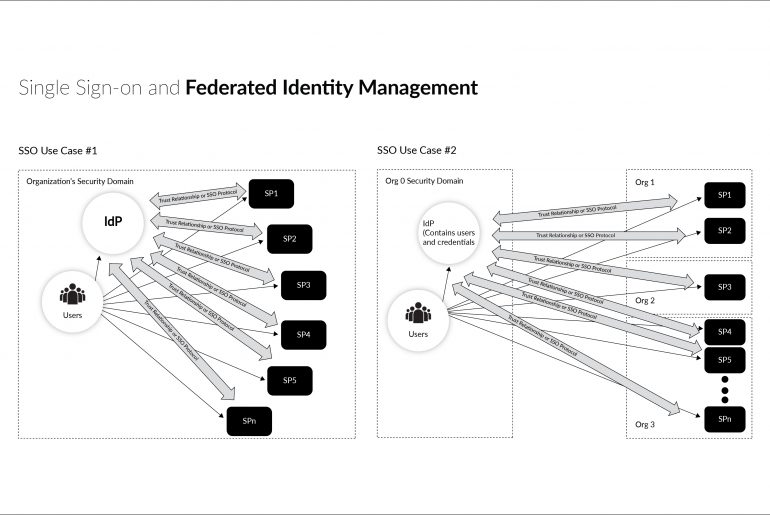
Migration to the cloud is no longer an emerging trend. It is now a well-established method of running the operations of a business. With the cloud, you can manage data and applications in a secure environment and ensure that your users face virtually no latency while using your applications. But although the cloud comes with a basic framework for security, it still has its inherent security risks which need highly specific cloud security solutions to reliably protect your data.
To understand the need for implementing an effective cloud security solution, a deeper understanding of what causes and constitutes a cloud security threat is important.
At most enterprises, data centers are a repository of information contained within a network of servers from where data is transmitted to other touch points for processing. While these data centers could be cloud-based or on-premise, the security of such business-critical data is of paramount importance.
There could be several vulnerabilities in your network in the form of entry points that seem like they can be ignored. While there are several measures you can implement to physically secure your data center, it takes a lot more to secure remote or even on-premise servers from virtual attacks. An effective data center security solution will allow you to intuitively monitor all the entry points for possible attacks and ensure that you are protected against any breach.
Company X is a leading automotive hardware manufacturer. In the competitive manufacturing environment, documentation of activity are standardization of processes are critical requirements.