When in action, a social engineering attack could look like an email received from a government organization or your own organization asking your employees to divulge their credentials. The basis of social engineering attacks is to induce fear or urgency in unsuspecting users and employees into handing over sensitive information. Over the years, these attacks have become more sophisticated – even if you open a mail or message from a possible attacker, malware is immediately installed on your system.
Identity theft is as real as your identity and as dangerous as the one who steals it. It occurs when an unauthorized person or entity uses your personal information to assume your identity and commit fraud and other criminal activities including stealing from you, or from others in your name.
What does an identity thief steal?
Your name, address, credit card or bank account information, and even information that might otherwise seem harmless, such as photographs, information about your family members or your date of birth could be used in harmful ways in the wrong hands.
Apart from data security, data privacy represents a major area of concern in IT security today. When it comes to data privacy, all organizations are very particular about where and how their company data is being saved, and who has access to it.
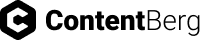
This is also related to one of the major reasons why organizations still hesitate to move their data to the cloud – “who else has access to my data if I move to cloud?” Even though almost every IaaS and PaaS provider tries to build confidence in their clients through certifications by authorized agencies, many enterprises are still not convinced. The reason is that there are still areas that lack transparency, where details on their data privacy are not clearly explained and conveyed to them.
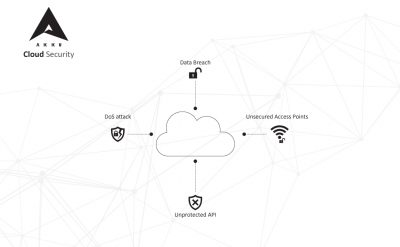
Migration to the cloud is no longer an emerging trend. It is now a well-established method of running the operations of a business. With the cloud, you can manage data and applications in a secure environment and ensure that your users face virtually no latency while using your applications. But although the cloud comes with a basic framework for security, it still has its inherent security risks which need highly specific cloud security solutions to reliably protect your data.
To understand the need for implementing an effective cloud security solution, a deeper understanding of what causes and constitutes a cloud security threat is important.