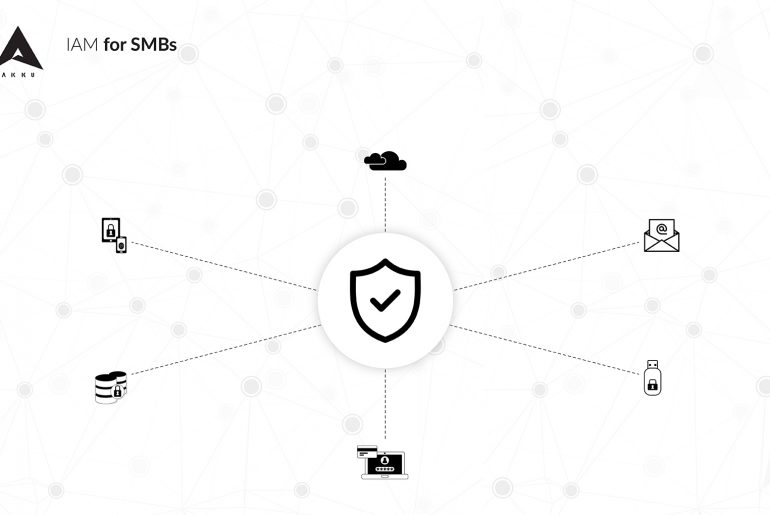
While it is natural to feel apprehensive on the cloud, especially if you are new to it, remember that there are a number of ways to stay in control of your organization’s applications and data, even while ensuring that authorized users can access them with greater ease.
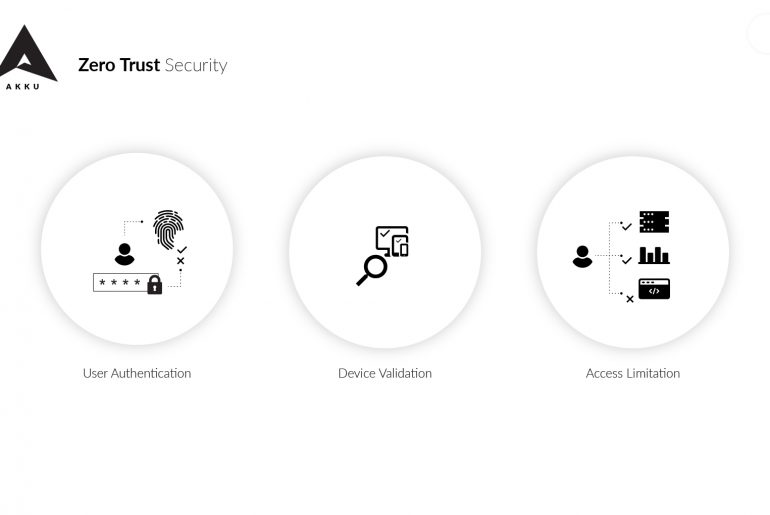
Here are 7 ways in which Akku, the Identity and Access Management (IAM) solution from CloudNow, can help you address security challenges