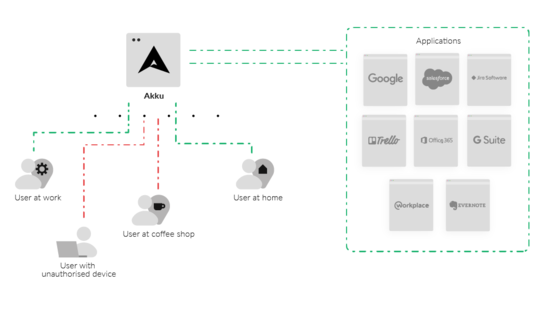
In today’s technology ecosystem, a strong foundation for authorization plays an important role in the overall data security of a company. Controlling each user’s access to data, and monitoring this across devices and browsers is essential to your enterprise’s security.
Implementing a strong device policy is an integral aspect of data security
With a strong device policy in place, it is possible to exercise highly granular control over which of the company’s applications, information, and data your employees can access– through the company’s devices, as well as through their personal devices.